- Unlimited Leave
- Posts
- 🗺️ Management & Governance Cloud Environment Guide
🗺️ Management & Governance Cloud Environment Guide
and you can now add 7 new regions to you Control Tower Landing Zone configuration
Happy 3rd winter from South Dakota. This is Unlimited Leave, the AWS Management and Governance newsletter that uses AI to generate its cover images. Caaan you teeel.
It’s not a lot but after 90 degrees a little over a week ago, we’ve been back to sub-freezing temps and flurries. I’m ready to walk the kid to the busy stop without a jacket.

This week's topics
You should start a newsletter
A Few Announcements
Management & Governance Cloud Environment Guide
More on GitLab OIDC for AWS
Price Increase for Greenfield Course
Start a Newsletter
Do I make this newsletter look easy?
If you said yes, it’s a lie. It’s all a lie.
For someone like me, putting this out every week is pretty hard. But it doesn’t have to be. I make it hard because that’s just the personality I have.
I don’t think the content is good enough
I don’t think I’m good enough
I struggle with prioritizing relationships and family, with work and side projects. Spoiler - my default is family and relationships.
However, beyond all of that, this is the best platform I’ve used, and being a technologist, I’ve tinkered with at least a half dozen others.
If you ever thought about creating a newsletter, I’d say this is the platform to use. I love that every email can be a post of a feed and I can make only posts if I want and not send them as emails.
A rising tide lifts all boats. It doesn’t have to be about AWS, although that would be great and I’d subscribe, but if you ever thought about creating a newsletter of your own, use this link 👇 and take BeeHiiv for a spin.
I started this and it quickly became more than I ever had imagined.
If you try and it’s not for you, the good news is, sinking ships lift all boats as well.
Announcements
In addition to the standard service announcements, I received an email in the root address for all of my Organization Management accounts indicating that there is going to be a change to how access denied error messages are presented when IAM resources bump up against Service Control Policies (SCPs).
Hello,
Beginning May 5, 2023, and rolling out over several weeks, AWS Identity and Access Management (IAM) will be changing access denied error messages for service control policies (SCPs) to be more intuitive, enabling you to understand when explicit versus implicit deny cases occur.
In the current IAM systems for SCPs, when access is denied due to the absence of explicit “Allow” statements (implicit deny case), it is reported as an explicit deny by the SCP as noted in our documentation [1]. We have been working on improving this experience. As a result, you will observe a more intuitive denial message where implicit denials in SCPs will be returned as implicit denials, instead of explicit denials. This does not have any impact on the final authorization result.
If you have workflows that are dependent on exact string matching of current error messages, we recommend you review them as IAM will begin reporting the new intuitive error message after May 5, 2023.M&G Environment Guide
After last week’s issue, I received an email from a reader who has recently pre-paid for the Greenfield AWS Organizations Deployment course. The reader asked, “Have I ever run through the AWS Well-Architected Management and Governance Lens and wondered if the content will align with AWS recommendations and best practices?”
Full transparency, I’ve never run through this specific guide from beginning to end. To be honest, I haven’t gone back through anything in the WAR since AWS added the Sustainability Pilar. Not that much (if anything) changed in the other pillars. It’s just been that long.
I have however run through WARs for customer accounts in a previous organization and will be responsible for completing them in my current setup.
Regarding the Greenfield Course content being aligned with the M&G Lens, yes, it will be aligned. Sort of. The copout is that the pillars and lens have a heavy focus on workload. That is where responsibility breaks off.
You are either responsible for infrastructure, applications, and workloads, or both in your organization. I do everything I can to pass the baton on the applications and workload stuff. The goal of the Greenfield course is to build a robust, well-architected, scalable foundation to more easily enable meeting the WAR recommendations for the applications and workloads.
There is some cross-over between the two. Monitoring, networking, security controls, and more. Unfortunately, a lot of the security framework controls assume everything is all rolled into one big package. The truth is that authentication to your AWS Accounts seldom has anything to do with how users or customers authenticate to applications or workloads.
The idea behind the Greenfield course is to create processes and guardrails to prevent those responsible for deploying the workloads and applications from even being able to use unencrypted resources or make instances directly exposed to the public for example. Unless you are truly responsible for the whole stack, there just isn’t time to police and run all of these reviews yourself.
The Greenfield course should help you deploy AWS Accounts with the governance and staged resources in place to aid in well-architected deployments.
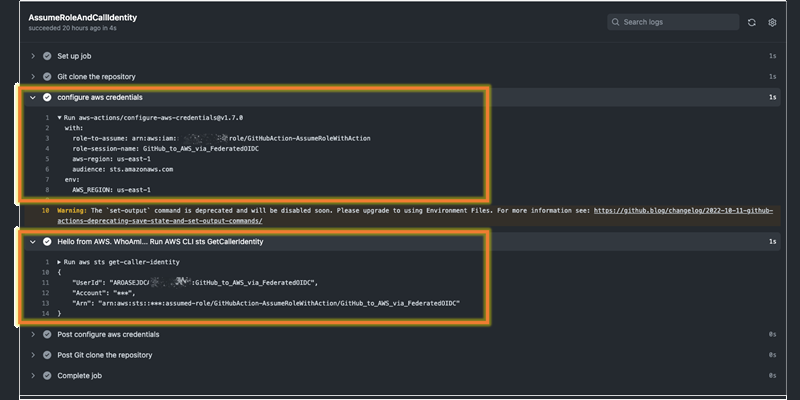
More on GitHub OIDC
This week, the AWS Security Blog released a new post walking through the deployment of the GitHub OIDC and Role. It’s a nicely done post with great detail you can check it out here.
If you want to skip all of that, I’ve packed a CloudFormation that will deploy the IDP and Role pair for you here:
and in the past, using IAM Users, shared some GitHub Action Workflows for the deployment of CloudFormation and Terraform here:
Price increase for Greenfield Course
Just like my electric bill, prices are on the rise. The same is true for the pre-sale price of the Greenfield AWS Organizations Deployment Course
Every week now, like a broken record, I am going to remind readers that over the next few weeks leading to the launch, the pre-sale price of the course is going to increase by $10 each week. As we get closer to launch, $20 per week. Until the launch of the course at $299.
March 31st - $99
April 7th. - $99
April 14th - $99
April 21st - $109
April 28th - $119